| 11-06 19:17:21.251 18416 18416 I RegisterNatives: java_class: com.meituan.android.common.mtguard.ShellBridge, name:main, sig:(I[Ljava/lang/Object;)[Ljava/lang/Object;, fnPtr:0x7762b2cd2c
11-06 19:17:21.277 18416 18416 I RegisterNatives: java_class: com.meituan.android.common.mtguard.MainBridge, name:main, sig:(I[Ljava/lang/Object;)[Ljava/lang/Object;, fnPtr:0x7762b320ac
|
| 7762b07000-7762cdf000 r-xp 00000000 103:01 3153157 /data/app/com.meituan.retail.v.android-D1zGmxl7VKa9wj3M9a9daQ==/lib/arm64/libmtguard.so
|
hex(0x7762b320ac-0x7762b07000)
Hmac_sha1
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
| const addr_hmac_sha1 = base.add(0x4B474);
Interceptor.attach(addr_hmac_sha1, {
onEnter: function (args) {
this.arg0 = args[0];
this.arg1 = args[1];
this.arg2 = args[2];
this.arg3 = args[3];
this.arg4 = args[4];
console.log(`[*] 参数0 (输入): ${this.arg0}`);
console.log(`[*] 参数1 (长度): ${this.arg1}`);
console.log(`[*] 参数2 (输入): ${this.arg2}`);
console.log(`[*] 参数3 (长度): ${this.arg3}`);
console.log(`[*] 参数4 (长度): ${this.arg4}`);
console.log(hexdump(this.arg0, 64));
console.log(hexdump(this.arg2, 64));
console.log(hexdump(this.arg4, 64));
var s = Memory.readCString(this.arg2)
console.log(s)
console.log("\n[*] 调用栈:");
console.log(Thread.backtrace(this.context, Backtracer.ACCURATE)
.map(DebugSymbol.fromAddress)
.slice(0, 10)
.join("\n"));
},
onLeave: function (retval) {
console.log('onLeave...')
console.log(hexdump(this.arg0, 32));
console.log(hexdump(this.arg2, 64));
console.log(hexdump(this.arg4, 64));
console.log(`retval: ${retval}`);
}
});
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
| (frida_latest) ➜ meituan_retail_sign git:(master) ✗ python injector.py test2.js
[*] 参数0 (输入): 0x77782cffd0
[*] 参数1 (长度): 0x24
[*] 参数2 (输入): 0x77c9f22800
[*] 参数3 (长度): 0x7b2
[*] 参数4 (长度): 0x785ef8c520
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
77782cffd0 7f 37 61 05 16 0a 5a 7c 63 3b 66 60 1a 5f 79 60 .7a...Z|c;f`._y`
77782cffe0 10 3c 67 14 0f 7b 1b 45 13 18 18 4b 1e 1a 42 24 .<g..{.E...K..B$
77782cfff0 3a 5d 1b 12 39 6f 2b 39 37 75 6f 3d 00 7d 00 00 :]..9o+97uo=.}..
77782d0000 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
77782d0010 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
77782d0020 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
77782d0030 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
77782d0040 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
77782d0050 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
77782d0060 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
77782d0070 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
77782d0080 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
77782d0090 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
77782d00a0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
77782d00b0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
77782d00c0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
77c9f22800 47 45 54 20 2f 61 70 69 2f 75 72 6c 2f 6c 6f 67 GET /api/url/log
77c9f22810 69 6e 5f 6d 61 69 63 61 69 61 70 70 20 4c 4f 47 in_maicaiapp LOG
77c9f22820 49 4e 5f 49 44 45 4e 5f 53 54 52 49 4e 47 3d 30 IN_IDEN_STRING=0
77c9f22830 30 30 30 30 30 30 30 30 30 30 30 30 45 33 33 36 000000000000E336
77c9f22840 35 38 44 36 30 39 30 30 34 35 44 30 41 35 32 45 58D6090045D0A52E
77c9f22850 38 38 43 46 41 38 44 33 44 30 33 38 41 31 37 32 88CFA8D3D038A172
77c9f22860 30 32 36 32 31 37 32 37 36 39 37 38 30 35 30 26 026217276978050&
77c9f22870 61 63 63 65 73 73 69 62 69 6c 69 74 79 5f 65 6e accessibility_en
77c9f22880 61 62 6c 65 64 3d 66 61 6c 73 65 26 6a 6f 69 6e abled=false&join
77c9f22890 6b 65 79 3d 31 30 30 32 30 33 5f 2d 31 31 37 35 key=100203_-1175
77c9f228a0 32 39 38 37 38 37 26 70 61 63 6b 61 67 65 4e 61 298787&packageNa
77c9f228b0 6d 65 3d 63 6f 6d 2e 6d 65 69 74 75 61 6e 2e 72 me=com.meituan.r
77c9f228c0 65 74 61 69 6c 2e 76 2e 61 6e 64 72 6f 69 64 26 etail.v.android&
77c9f228d0 72 69 73 6b 5f 73 6d 73 50 72 65 66 69 78 49 64 risk_smsPrefixId
77c9f228e0 3d 31 31 26 72 69 73 6b 5f 73 6d 73 54 65 6d 70 =11&risk_smsTemp
77c9f228f0 6c 61 74 65 49 64 3d 36 26 73 64 6b 56 65 72 73 lateId=6&sdkVers
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
785ef8c520 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
785ef8c530 00 00 00 00 00 00 00 00 43 00 67 7a 77 00 00 00 ........C.gzw...
785ef8c540 63 6f 6d 2e 61 6e 64 72 6f 69 64 2e 70 72 6f 76 com.android.prov
785ef8c550 69 64 65 72 73 2e 63 61 6c 65 6e 64 61 72 00 00 iders.calendar..
785ef8c560 01 00 00 00 00 00 00 00 01 00 00 00 00 00 00 00 ................
785ef8c570 fe ff ff ff 00 00 00 00 42 00 f8 c9 77 00 00 00 ........B...w...
785ef8c580 6d 65 69 74 75 61 6e 31 73 61 6e 6b 75 61 69 30 meituan1sankuai0
785ef8c590 00 ff ff ff 00 00 00 00 76 00 00 00 00 00 00 00 ........v.......
785ef8c5a0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
785ef8c5b0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
785ef8c5c0 6d 65 69 74 75 61 6e 30 73 61 6e 6b 75 61 69 31 meituan0sankuai1
785ef8c5d0 00 ff ff ff 00 00 00 00 5e 00 f8 5e 78 00 00 00 ........^..^x...
785ef8c5e0 63 6f 6d 2e 61 6e 64 72 6f 69 64 2e 70 72 6f 76 com.android.prov
785ef8c5f0 69 64 65 72 73 2e 63 61 6c 65 6e 64 61 72 00 00 iders.calendar..
785ef8c600 63 6f 6d 2e 74 65 6e 63 65 6e 74 2e 6d 6d 3a 70 com.tencent.mm:p
785ef8c610 75 73 68 00 65 72 20 74 68 72 65 61 64 20 30 00 ush.er thread 0.
GET /api/url/login_maicaiapp LOGIN_IDEN_STRING=0000000000000E33658D6090045D0A52E88CFA8D3D038A172026217276978050&accessibility_enabled=false&joinkey=100203_-1175298787&packageName=com.meituan.retail.v.android&risk_smsPrefixId=11&risk_smsTemplateId=6&sdkVersion=5.116.2-wz&supportReopen=true&utm_medium=android&utm_term=68600&uuid=0000000000000E33658D6090045D0A52E88CFA8D3D038A172026217276978050&version_name=6.86.0{"a0":"3.0","a1":"0a03b816-c295-46cc-ad01-f2a3704ce24f","a3":25,"a4":1762623078,"a5":"IyJsBWax75bUgOAHaje7xs/xVtp5u6/I6IdHDiQd3N/qXZU4xkEcH4O043Gv/ZvPjNwRF0Bj/mh1aB2n7JGOv2JqSXWbzMgEYZozOw27jXzM2T8NcmqxaJNhXLVyA7uDi8eE2zyZ09V3lALvw3oir2i8oqgRR3su7MJq+demXLhM1Z+HdnzSTvFWCtuRRVexClVh20d0t+L4b5genNY3mwomqY8lpX+7eiW8/TXsg1++VEkqGKOHWJR2a0HtnRKF+M+Uu5CoI+I1PpmNLK3ggRte0gzs3hz4QxwSAghGYc9ewVwfZTxMRb/GrQRAAGFIYi/KMW/XY7K6hysjDh458UP2UqSze61f+xAHW7dauMUXEyTAmYbDb9jhrPRm2ws=","a6":0,"a7":"1Oy6N74EtO7R81J01Zwu1/GQSYlNtIiu4wOtRUrhCvJWJk67hMFPW/717YC7J0k7UOceW2sr6D0xHhePpSFNsh+3EIyxyRN7P6yL86I0hDw=","a8":"9f5c7593a3bdb90bdcf9e15832ef24af3982f568c45cb8d73709b7c2","a9":"8a6079a0lPjcsBrMRvE8JjeNVGh1CX28oDwwEctMFwNmi+S2YoKTPy0CDjkTRtGimdvgS2/+eYwFaB8fXUo+ftwDNYYryhdWc8eQdjc4ZnD504GfbL5VBpgAAzMw0YPVi5tnbWzz3H+Mh0A0kxyliDzubK7be9x5dOqznqKiTgLlnJack/CrgJaUMmtHelq8pKsjeIbKNLLG/z/k/vWXy5xg3D5ONNG266YDcv27pyPgzkeE4c4ybMimdyZCQP7pEfGB7KYXN4RzyEqdrnaVzxSKu0VQLd5nzwjpFUEE3LOAZOfPiqZ5B48nlmg43zTORaaHdOEWo7/nRSa2OfstiwMFf6KyF5gRYgUaRk05XgYtBgIJft4Ze1BnGs8CuhVChrTvu8abGj+n1qIs6wZTkduHedT56iTI4hU3OqzbSbE3hrSVSoDRfwo/aGKFcvpt8iV/1P6kJ30H4gL41r+DkQ0u2aqEwMu6Dg8gYZBZwpbQ+4nx2UL+d4RI4+NYs3bMH7Y8IW7+YdLAslYOLugyHu2hDprLMogjRT4e8+koL2UbOs3FHErHCvea9EIIgpT06HEQNU4YMj9qOPEmuotr1m4skeowwz0Llox0EiBnXehL4UcSFP5/CNwPAiicA/+1Iu0dhmeudHV+UrxJabNLckQkjUPpjQYb59n07+YbF6UJSrULqbLGD2CWo4sCg6vb7AA+W3+ERM+3pyNPRy9PynLm1/dBCMeiqMoP2I2jATIQHDfZaMrNPgn6wFcSzkSqemObr03EKRjmUlSqipESQFpSnEvxoIiJqswPDZaZoNlodCuiq3m4Oehe2N+PmQ4T1FcqEeUW68xZ/Lbhbejmfiae3yMgTg==","a10":"5,29,1.1.1","x0":1}
[*] 调用栈:
0x777a610050 libmtguard.so!0x148050
0x777a60b8d0 libmtguard.so!0x1438d0
0x777a5dbed8 libmtguard.so!0x113ed8
0x777a5dbed8 libmtguard.so!0x113ed8
onLeave...
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
77782cffd0 7f 37 61 05 16 0a 5a 7c 63 3b 66 60 1a 5f 79 60 .7a...Z|c;f`._y`
77782cffe0 10 3c 67 14 0f 7b 1b 45 13 18 18 4b 1e 1a 42 24 .<g..{.E...K..B$
77782cfff0 3a 5d 1b 12 39 6f 2b 39 37 75 6f 3d 00 7d 00 00 :]..9o+97uo=.}..
77782d0000 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
77782d0010 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
77782d0020 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
77782d0030 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
77782d0040 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
77782d0050 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
77782d0060 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
77782d0070 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
77782d0080 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
77782d0090 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
77782d00a0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
77782d00b0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
77782d00c0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
77c9f22800 47 45 54 20 2f 61 70 69 2f 75 72 6c 2f 6c 6f 67 GET /api/url/log
77c9f22810 69 6e 5f 6d 61 69 63 61 69 61 70 70 20 4c 4f 47 in_maicaiapp LOG
77c9f22820 49 4e 5f 49 44 45 4e 5f 53 54 52 49 4e 47 3d 30 IN_IDEN_STRING=0
77c9f22830 30 30 30 30 30 30 30 30 30 30 30 30 45 33 33 36 000000000000E336
77c9f22840 35 38 44 36 30 39 30 30 34 35 44 30 41 35 32 45 58D6090045D0A52E
77c9f22850 38 38 43 46 41 38 44 33 44 30 33 38 41 31 37 32 88CFA8D3D038A172
77c9f22860 30 32 36 32 31 37 32 37 36 39 37 38 30 35 30 26 026217276978050&
77c9f22870 61 63 63 65 73 73 69 62 69 6c 69 74 79 5f 65 6e accessibility_en
77c9f22880 61 62 6c 65 64 3d 66 61 6c 73 65 26 6a 6f 69 6e abled=false&join
77c9f22890 6b 65 79 3d 31 30 30 32 30 33 5f 2d 31 31 37 35 key=100203_-1175
77c9f228a0 32 39 38 37 38 37 26 70 61 63 6b 61 67 65 4e 61 298787&packageNa
77c9f228b0 6d 65 3d 63 6f 6d 2e 6d 65 69 74 75 61 6e 2e 72 me=com.meituan.r
77c9f228c0 65 74 61 69 6c 2e 76 2e 61 6e 64 72 6f 69 64 26 etail.v.android&
77c9f228d0 72 69 73 6b 5f 73 6d 73 50 72 65 66 69 78 49 64 risk_smsPrefixId
77c9f228e0 3d 31 31 26 72 69 73 6b 5f 73 6d 73 54 65 6d 70 =11&risk_smsTemp
77c9f228f0 6c 61 74 65 49 64 3d 36 26 73 64 6b 56 65 72 73 lateId=6&sdkVers
0 1 2 3 4 5 6 7 8 9 A B C D E F 0123456789ABCDEF
785ef8c520 e4 1c 2b 75 d8 20 06 aa 02 35 6b cf a8 ef 2e 40 ..+u. ...5k....@
785ef8c530 07 ad 5f 39 00 00 00 00 43 00 67 7a 77 00 00 00 .._9....C.gzw...
785ef8c540 63 6f 6d 2e 61 6e 64 72 6f 69 64 2e 70 72 6f 76 com.android.prov
785ef8c550 69 64 65 72 73 2e 63 61 6c 65 6e 64 61 72 00 00 iders.calendar..
785ef8c560 01 00 00 00 00 00 00 00 01 00 00 00 00 00 00 00 ................
785ef8c570 fe ff ff ff 00 00 00 00 42 00 f8 c9 77 00 00 00 ........B...w...
785ef8c580 6d 65 69 74 75 61 6e 31 73 61 6e 6b 75 61 69 30 meituan1sankuai0
785ef8c590 00 ff ff ff 00 00 00 00 76 00 00 00 00 00 00 00 ........v.......
785ef8c5a0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
785ef8c5b0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
785ef8c5c0 6d 65 69 74 75 61 6e 30 73 61 6e 6b 75 61 69 31 meituan0sankuai1
785ef8c5d0 00 ff ff ff 00 00 00 00 5e 00 f8 5e 78 00 00 00 ........^..^x...
785ef8c5e0 63 6f 6d 2e 61 6e 64 72 6f 69 64 2e 70 72 6f 76 com.android.prov
785ef8c5f0 69 64 65 72 73 2e 63 61 6c 65 6e 64 61 72 00 00 iders.calendar..
785ef8c600 63 6f 6d 2e 74 65 6e 63 65 6e 74 2e 6d 6d 3a 70 com.tencent.mm:p
785ef8c610 75 73 68 00 65 72 20 74 68 72 65 61 64 20 30 00 ush.er thread 0.
|
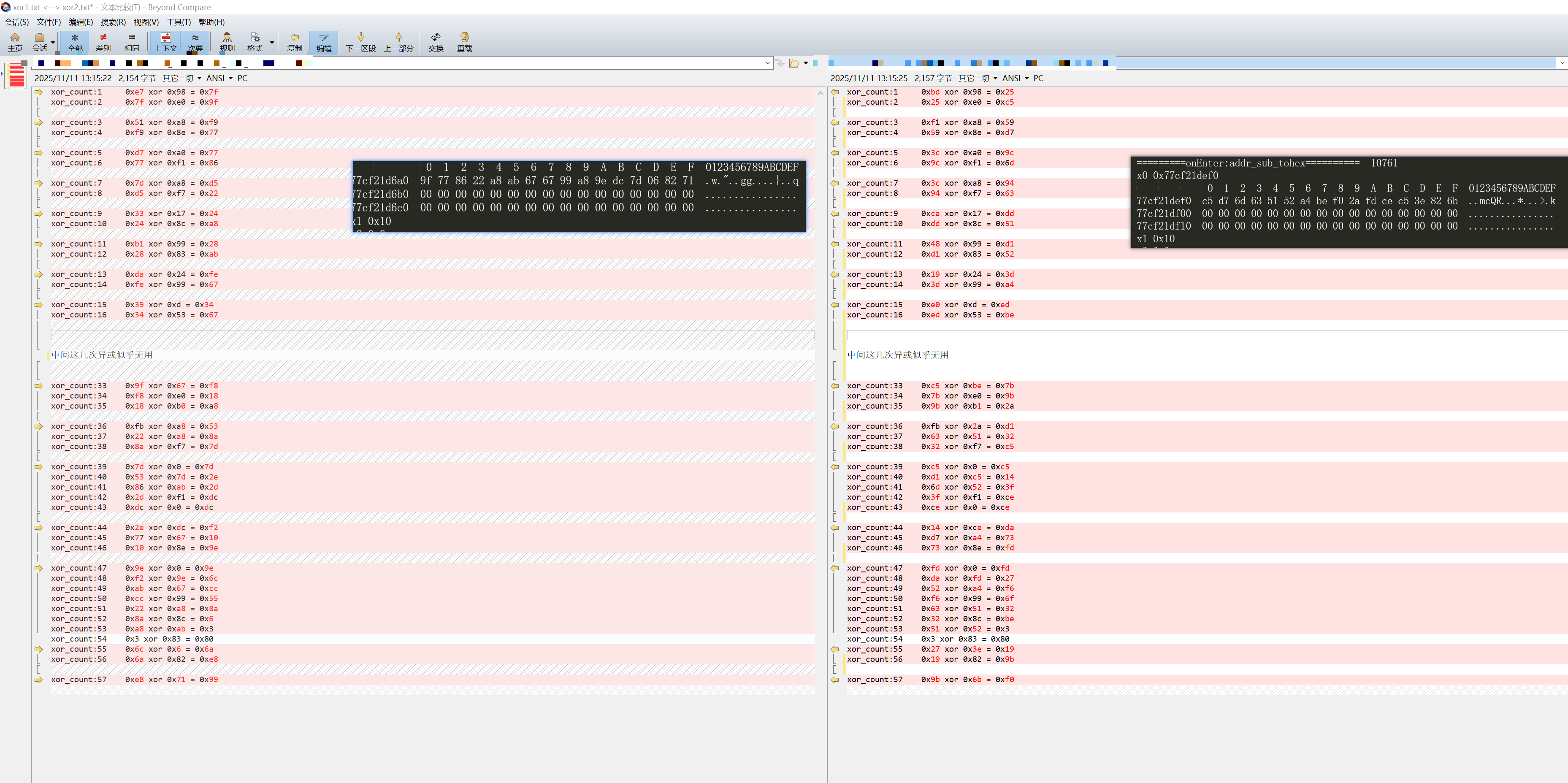
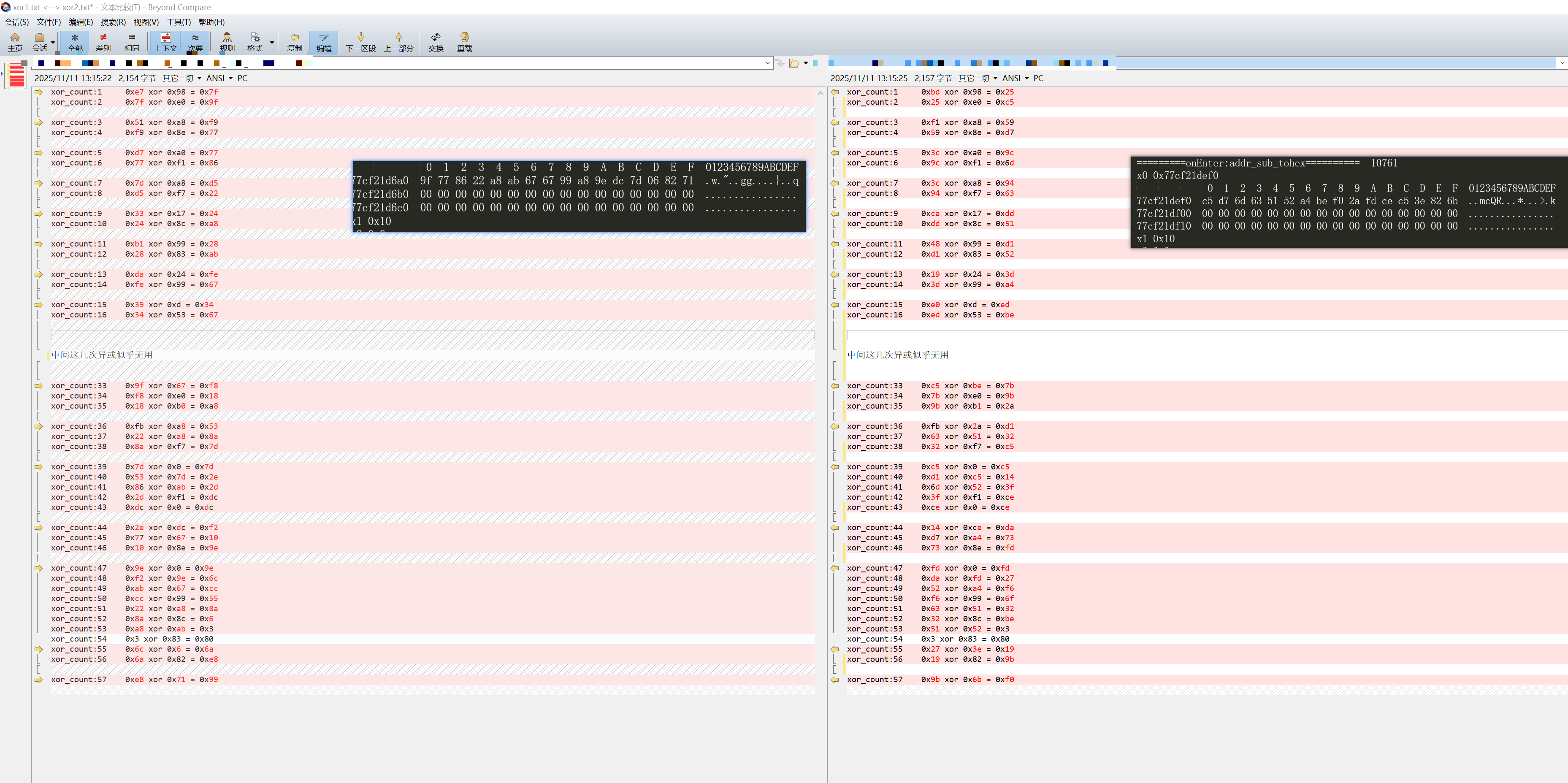
mtgsig3.0 a2 生成
- 计算hmac_sha1密钥
- 计算hamc_sha1哈希,结果为0x14字节hash值
- AES加密hash值,标准的AES-ECB加密,需要将hash填充到0x20字节,加密结果也是0x20字节。
- 取AES加密的前0x8字节,与密钥进行一系列异或运算,得到新的8个字节数据。
- 为上一步的8字节生成校验数据,
| [0x98, 0xa8, 0xa0,0xa8,0x17,0x99, 0x24,0x0d, 0xcd,0xc6, 0xca,0x6a,0x75,0xda,0x36,0xea, ]
|
BR X8混淆
指令解析
| ADRP X26, #off_1F7230@PAGE
ADD X26, X26, #off_1F7230@PAGEOFF
|
这两条指令是 ARM64 中加载 64 位地址的标准方法:
ADRP (Address of Page)
| ADRP X26,
加载 off_1F7230 的页地址(4KB 对齐)到 X26
页地址 = off_1F7230 & 0xFFFFFFFFFFFFF000(清除低 12 位)
例如:如果 off_1F7230 = 0x1F7230,则 X26 = 0x1F7000
|
ADD (加上页内偏移)
| ADD X26, X26, #off_1F7230@PAGEOFF
将页内偏移(低 12 位)加到 X26
页内偏移 = off_1F7230 & 0xFFF
例如:0x230
最终:X26 = 0x1F7000 + 0x230 = 0x1F7230
|
为什么要分两步?
ARM64 的指令是 32 位固定长度,无法在一条指令中编码完整的 64 位地址。所以:
ADRP 加载高位(页地址)
ADD 加上低 12 位(页内偏移)
完整混淆指令
| .text:000000000004B4D0 CMP W27, #0 ; 比较 W27 是否为 0
.text:000000000004B4D4 ADRP X26, #off_1F7230@PAGE ; X26 = off_1F7230 的页地址
.text:000000000004B4D8 STR X9, [X24,#0xE8] ; 保存 X9(无关)
.text:000000000004B4DC CSEL X8, X8, XZR, NE ; X8 = (W27
XZR (Zero Register) 是 ARM64 的零寄存器,永远返回 0。
.text:000000000004B4E0 ADD X26, X26, #off_1F7230@PAGEOFF ; X26 = off_1F7230 完整地址
.text:000000000004B4E4 LDR X8, [X26,X8] ; X8 = [off_1F7230 + X8] 从跳转表读取地址
.text:000000000004B4E8 MOV W9, #0x5AE ; W9 = 0x5AE
.text:000000000004B4EC MOV W10, #0xAE47 ; W10 = 0xAE47
.text:000000000004B4F0 CSEL X9, X10, X9, NE ; X9 = (W27
X8 = X8 - X9
.text:000000000004B4F8 MOV X23, X1 ; 保存 X1(无关)
.text:000000000004B4FC BR X8 ; 跳转到 X8
|
逻辑分析
这是一个基于条件的双路跳转表混淆:
如果 W27 != 0(条件为真):
X8 = 0x10
X8 = [off_1F7230 + 0x10] ← 从跳转表读取地址
X9 = 0xAE47
X8 = X8 - 0xAE47
BR X8 → 跳转到目标1
如果 W27 == 0(条件为假):
X8 = 0
X8 = [off_1F7230 + 0] ← 从跳转表读取地址
X9 = 0x5AE
X8 = X8 - 0x5AE
BR X8 → 跳转到目标2
计算目标地址需要:
查看 off_1F7230 处的数据(跳转表)
读取 [off_1F7230 + 0] 和 [off_1F7230 + 0x10] 的值
分别减去 0x5AE 和 0xAE47